Network Diagram
Network isolation
The network diagram above is used for every project (staging-nl, production-nl, production-ch). Each environment has its own VPN gateway, load balancer and VPC network.
Account isolation
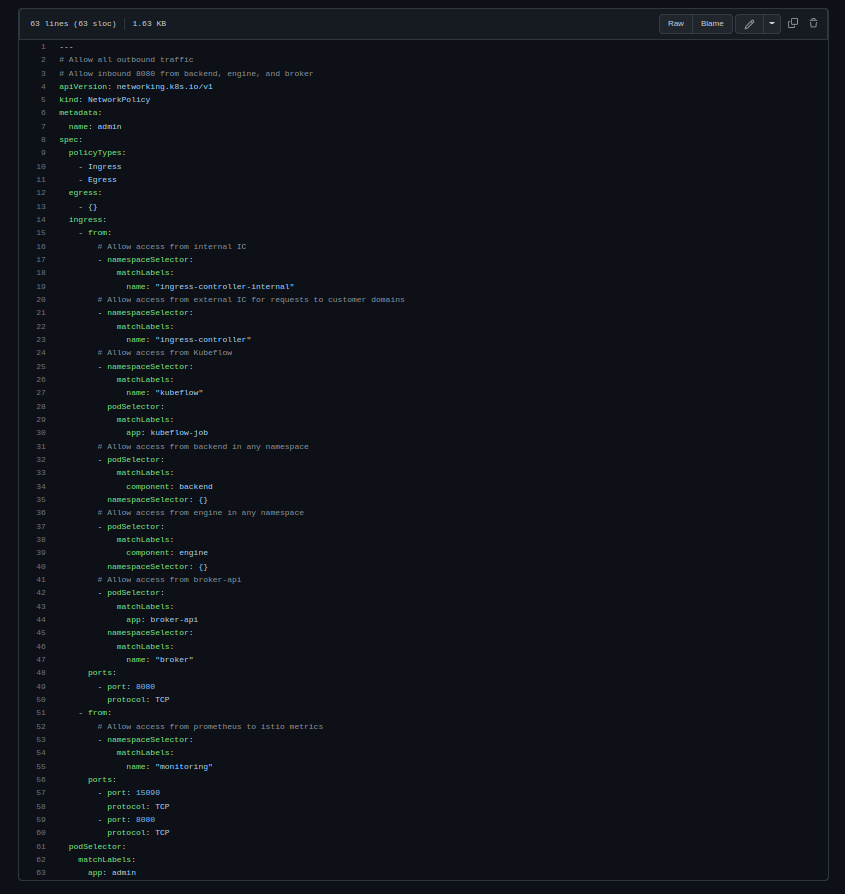
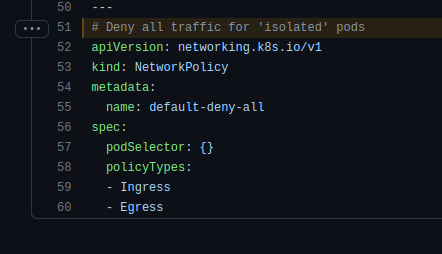
Customer accounts all have their own kubernetes namespace. Each namespace have NetworkPolicies in place that allow only the minimal traffic needed for all services to function and communicate (Examples: 1, 2, 3). Every namespace has a default NetworkPolicy that denies all traffic from all namespaces (link).
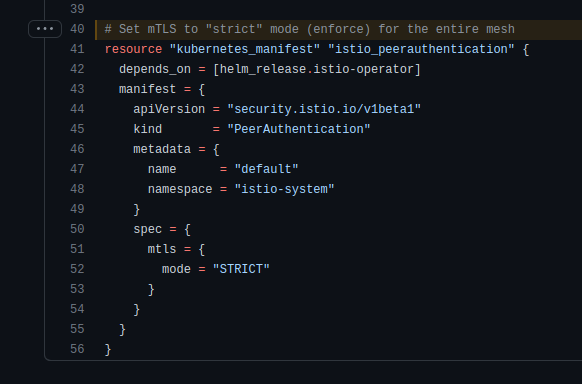
Besides NetworkPolicies, we also use Istio service mesh to enforce mTLS between all our services. It's not possible to communicate with services of other accounts. Istio and Istio mTLS is enforced on every service (link). Services not part of the mesh cannot communicate with services inside the mesh.